Hello hackers the objective for this article is to making your system anonymous by tunneling your traffic via proxychains and tor.
Also you need to keep this important thing in mind that if you are using a name server that is provided by you local isp you have potential threats of getting you geolocation leaked. So follow what i guide you though the rabbit hole !!!

How to make yourself Anonymous using Proxychain and Tor
What is Tor ?
The Onion Router, or Tor, is a free and open-source programme that facilitates anonymous communication by routing Internet traffic over a global, volunteer overlay network made up of over 7,000 relays.
What is Proxychains ?
Essentially serving as “middlemen” for incoming and outgoing network traffic.
ProxyChains is a network address translation tool that enhances privacy and anonymity in online communications by managing a chain of proxies that can be tailored to provide better security, privacy, and performance.
Proxychains Installation
To install proxchains on you local system type:
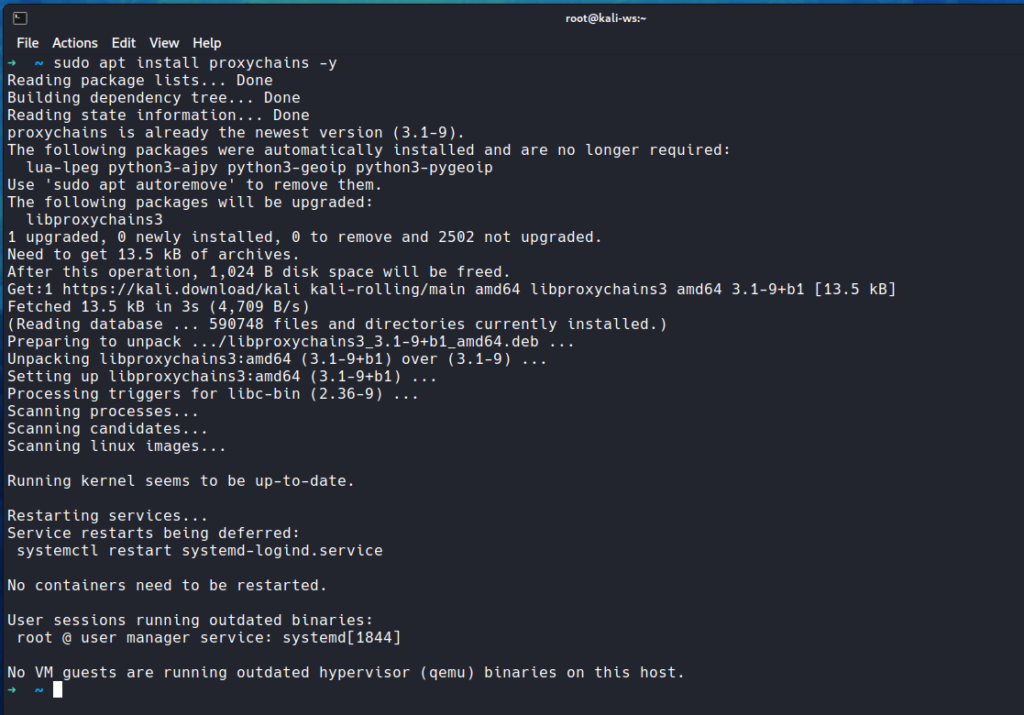
sudo apt install proxychains -y
To install tor service on your local system type:
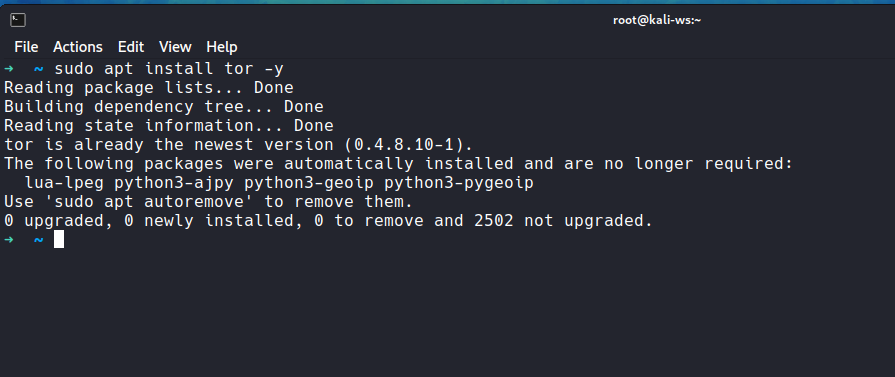
sudo apt install tor -y
Configuring the configuration file
In order to manage you need to edit the configuration file so type:
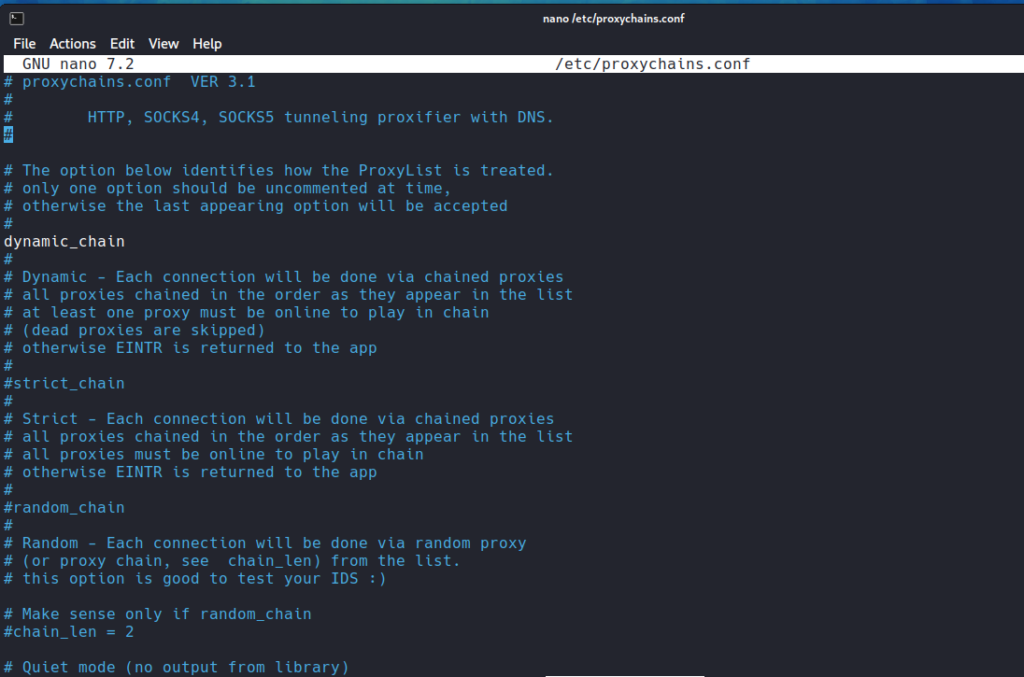
sudo vim /etc/proxychain.conf
Different type of chains
So you can see and study what Dynamic And Static chains are
Dynamic Chain
With the help of the “dynamic chain,” we may route our traffic through each proxy on the list; if a proxy is unavailable, it will be skipped and immediately routed to the next one.
Static Chain
Strict chain: All proxies in the list will be used and chained in the assigned order
Random Chain
Random Chain: All proxies in the list are used randomly .
Whenever you use a sock proxy the network is realtively slower so you can edit the timeouts to chahge the chains.
Come down to the proxy list and here you can edit the proxy:
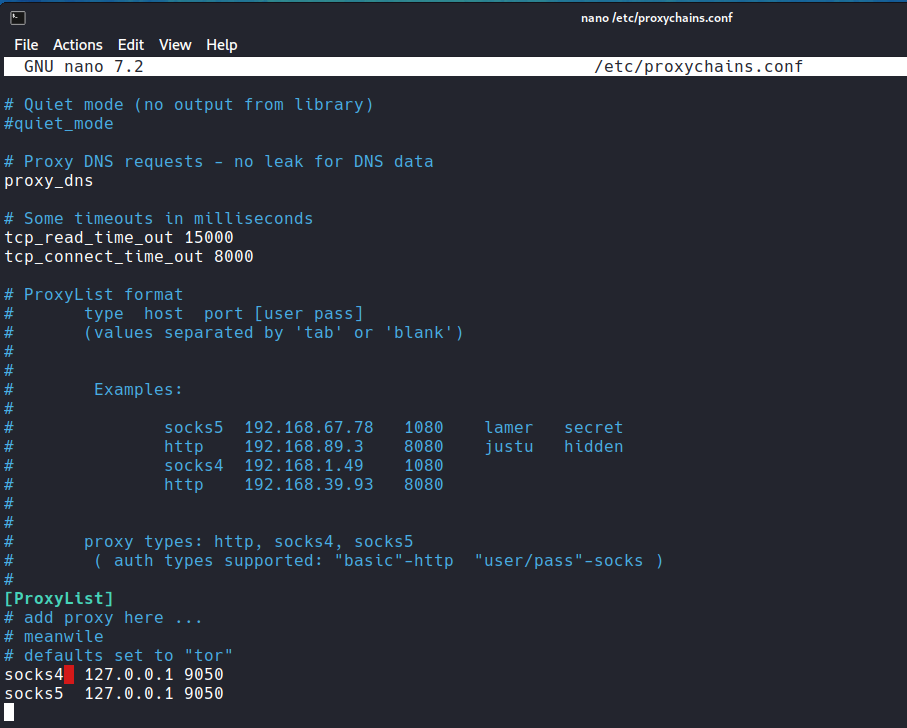
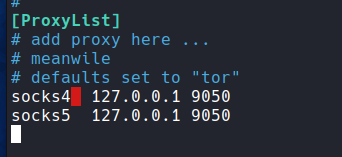
for instance to add a sock4,sock5 proxy type
sock4 127.0.0.1 9050
sock5 127.0.0.1 9050
What is Sock proxy ? Port 9050
Tor listens for client connections on port 127.0. 0.1:9050 by default; this port, also referred to as the “SocksPort,” enables client apps to connect to Tor and route their traffic through the Tor network.
One sort of proxy server that transfers downloaded data as though it were coming from a remote server is called a socks proxy.
Socks proxies differ from traditional HTTP or HTTPS proxies in that they do not require clients to change their socket connections or disconnect and reconnect for every HTTP request.
Now you need to enable the Tor service
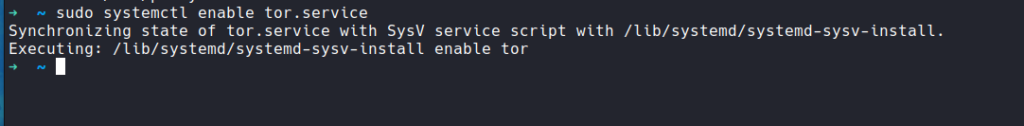
sudo systemctl enable tor.service
Now start the service
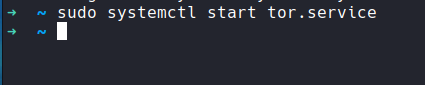
sudo systemctl start tor.service
And check the status via
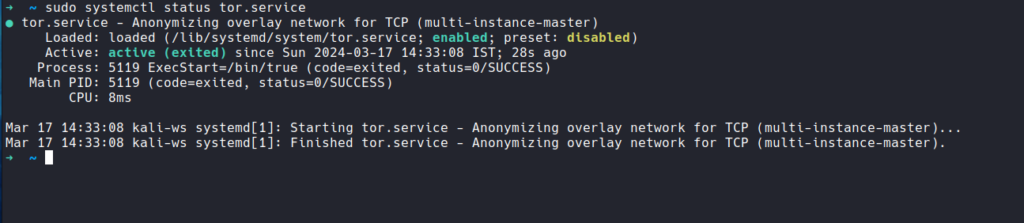
sudo systemctl status tor.service
Testification
In order to test whatever configuration you made use the following command to bind and use firefox with proxychain
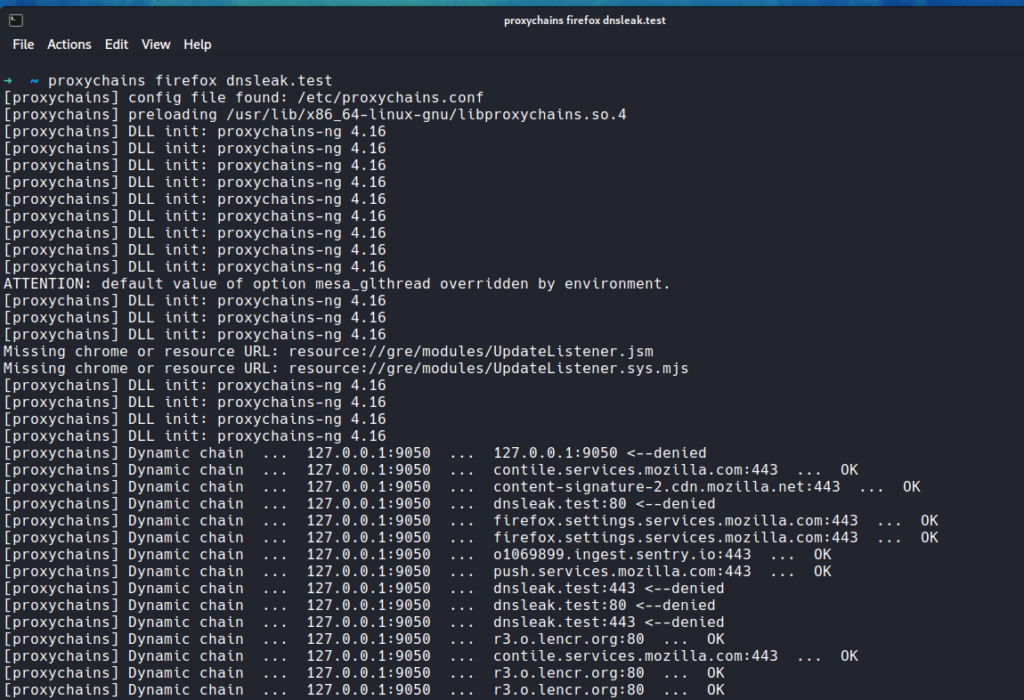
proxychains firefox dnsleak.test
dnsleak.test will test you if your dns is leaking geolocation.
As you see it has changed the IP.
Using with nmap
Sudo proxychains nmap -sS -sV 192.168.1.1
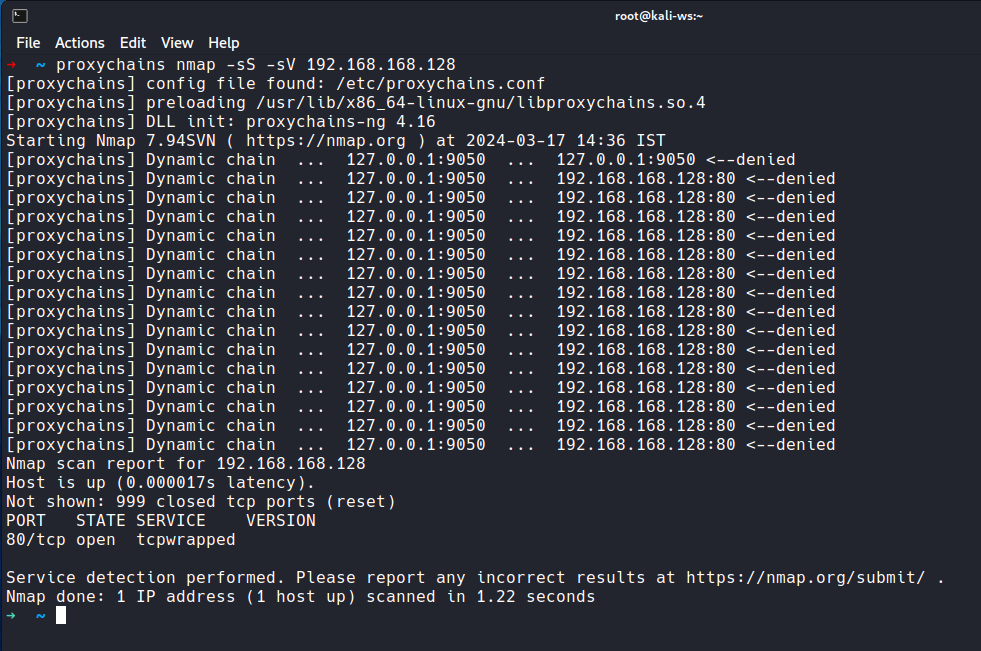
So it is working !!!
So yeah that is it hackers for todays video and i’ll see you in the next interesting article.
So learn more and don’t forget to check our blogs we keep updating the content daily .
Happy Hacking Hackers !!!
Frequently Asked Questions
- What is Proxychain and Tor?
Proxychain is a tool that allows you to route your internet traffic through multiple proxy servers, while Tor is a free, open-source software that helps you protect your online privacy by routing your internet traffic through a network of volunteer-run servers. - Why would I want to make myself anonymous using Proxychain and Tor?
Making yourself anonymous can help protect your online privacy and security, prevent tracking of your online activities, and bypass censorship or geo-restrictions. - Is it legal to use Proxychain and Tor to make myself anonymous?
Yes, it is legal to use Proxychain and Tor to protect your online privacy and security. However, it is important to note that illegal activities are still illegal, even if you attempt to hide your identity. - How do I set up Proxychain and Tor?
To set up Proxychain, you simply need to configure it to route your internet traffic through multiple proxy servers. To set up Tor, you need to download the Tor browser and connect to the Tor network. - How does Proxychain work?
Proxychain works by routing your internet traffic through a chain of proxy servers, which helps to mask your real IP address and location. - Can I use Proxychain and Tor on any device?
Yes, you can use Proxychain and Tor on most devices, including computers, smartphones, and tablets. - Are there any drawbacks to using Proxychain and Tor?
One drawback of using Proxychain and Tor is that it can slow down your internet connection due to the additional routing of internet traffic. - Can Proxychain and Tor completely make me anonymous online?
While Proxychain and Tor can help increase your online anonymity, it is important to remember that no method is foolproof and there may still be ways for your online activities to be traced. - How can I test if Proxychain and Tor are working correctly?
You can test if Proxychain and Tor are working correctly by visiting websites that detect your IP address and location, and confirming that they show a different IP address and location than your real one. - Are there any additional steps I can take to further protect my online anonymity?
In addition to using Proxychain and Tor, you can also use encryption tools, enable strict privacy settings on your devices and accounts, and be cautious about the information you share online.